Introduction
For agency owners and web professionals managing client sites with premium, gated, or confidential content, ensuring its exclusivity is paramount. Whether it's training videos, client documents, or exclusive reports, the value of such content is directly tied to its controlled distribution. However, even with robust access systems, the risk of unauthorised link sharing remains a persistent challenge.
A single authorised user sharing their access link can quickly lead to widespread, illicit distribution, undermining content value, revenue models, and data security. This article delves into the critical role of rate limiting as a proactive defence, particularly when coupled with secure WordPress token based access, to prevent such abuse and maintain stringent WordPress content access security.
The Challenge of Unauthorised Content Distribution
Imagine a scenario where a client has invested in a premium online course, only for a single participant to share their access link with a dozen others. Or a professional services firm distributing a confidential industry report to vetted partners, only to find the secure download link circulating freely.
These situations highlight a fundamental vulnerability: even if you implement login barriers or sophisticated token generation, the token itself can be shared. The consequences extend beyond simple content theft, impacting:
- Revenue Protection: For paid content, uncontrolled sharing directly translates to lost sales and devalued offerings.
- Intellectual Property: Proprietary data, research, or creative works lose their competitive edge when widely accessible without permission.
- Compliance and Confidentiality: For sensitive client documents or internal knowledge bases, unauthorised access can lead to severe data breaches and regulatory non-compliance.
- Brand Reputation: A perception of lax security can erode trust among legitimate users and clients.
Addressing this requires more than just generating secure links; it demands control over how those links are used.
Understanding Token-Based Access for WordPress Content
Before diving into rate limiting, it's crucial to grasp the mechanics of token-based access. Instead of relying solely on user logins, token-based systems provide a unique, cryptographically secure string – an "access token" – that grants temporary permission to specific content. When a user requests access to gated content, a token is generated and delivered to them, often via email.
Upon clicking the access link, the system validates the token. This validation typically checks several factors:
- Authenticity: Is it a legitimate token generated by the system?
- Integrity: Has the token been tampered with?
- Scope: Does it grant access to the specific resource being requested?
- Validity: Is the token still active and within its allowed time frame?
For robust security, solutions like WordPress Gatekeeper Pro utilise HMAC token WordPress implementations. HMAC (Hash-based Message Authentication Code) tokens are cryptographically signed, making them incredibly difficult to forge or alter without detection. This ensures that only tokens genuinely issued by your system can grant access, providing a strong foundation for WordPress content access security.
The Critical Role of Rate Limiting in Content Security
While HMAC tokens and expiry dates (WordPress access token expiry) are essential, they don't fully prevent link sharing. A legitimate, unexpired token can still be copied and distributed. This is where rate limiting steps in as a vital defence mechanism.
Rate limiting restricts the number of times a specific token can be used within a defined period. Instead of just checking if a token is valid, it also checks if that token has been used too frequently. For example, you might configure a token to be used a maximum of 5 times per hour, or 20 times per day.
If a token exceeds this usage threshold, subsequent access attempts are blocked, even if the token is otherwise valid and unexpired. This effectively curtails the impact of a shared link, limiting its utility to unauthorised users and protecting your valuable content from widespread abuse.
Implementing Effective Rate Limiting Strategies for WordPress
For agencies and web professionals, integrating rate limiting effectively into client sites requires a strategic approach. Here are key considerations and best practices:
Configurable Usage Limits
The ability to define precise usage limits is crucial. A "one-size-fits-all" approach rarely works. Consider the nature of the content:
- Client Documents: A highly sensitive document might have a very strict limit, perhaps 2-3 uses per day, to prevent casual sharing.
- Training Videos: For a course that users might revisit multiple times, a more generous limit like 10-15 uses per hour or 50 per day might be appropriate.
- Lead Magnet Downloads: If the goal is lead generation, a slightly higher limit might be acceptable, as the primary objective is capturing leads, not strict content control post-download.
Solutions like WordPress Gatekeeper Pro offer configurable rate limiting, allowing you to set these thresholds globally or even per-post, providing the flexibility needed for diverse content strategies.
Per-Token Tracking and Enforcement
Effective rate limiting operates on a per-token basis, not just per IP address. This is critical because a shared link could be accessed by multiple users from different IPs. The system needs to uniquely identify and track each individual token's usage. When a user (or multiple users with a shared token) attempts to access content:
- The system receives the access request along with the token.
- It validates the token's authenticity and expiry.
- It then checks the usage history for that specific token within the defined time window.
- If the usage count exceeds the configured limit, access is denied, and the user is typically presented with a message indicating the limit has been reached.
This granular approach ensures that even if one token is compromised, its impact is contained.
Combining Rate Limiting with Token Expiry
Rate limiting is most powerful when combined with a robust WordPress access token expiry strategy. Token expiry (Time-to-Live or TTL) defines how long a token remains valid. For example, a token might expire after 7 days, 30 days, or even indefinitely for certain client portal scenarios.
- Short-Term Access: For one-off downloads or time-sensitive content, a short expiry (e.g., 24-48 hours) coupled with strict rate limiting offers excellent control.
- Long-Term Access: For ongoing resources like a client's document library, a longer expiry (e.g., 365 days or unlimited) might be appropriate. Here, rate limiting becomes even more crucial to prevent continuous, uncontrolled sharing over an extended period.
The synergy between expiry and rate limiting creates a layered security model, significantly enhancing WordPress content access security.
Leveraging a Secure Proxy Endpoint for File Access
When protecting files and videos, simply linking to them won't work. A secure system streams content through a proxy endpoint. This endpoint acts as a gatekeeper, intercepting all requests for protected content.
- Token Validation: Before serving any file or video, the proxy endpoint rigorously validates the provided access token.
- Rate Limiting Enforcement: It's at this proxy endpoint where the WordPress rate limiting file access rules are applied. If the token's usage exceeds its limit, the proxy will refuse to stream the content.
- Secured Storage: Files are stored in a secured directory, often with randomised filenames and .htaccess blocking, making direct URL access impossible. All access must go through the token-validated proxy.
WordPress Gatekeeper Pro employs such a proxy endpoint, ensuring that every request for gated content passes through its token validation and rate limiting mechanisms.
Best Practices for Agencies and Client Content Security
As an agency or web professional, advise your clients on these best practices:
- Educate Users: Clearly communicate acceptable use policies for gated content. Inform users that access links are unique to them and sharing may result in access revocation.
- Monitor Access Patterns: Regularly review access analytics. Tools like Gatekeeper Pro's admin dashboard provide insights into token usage, helping identify potential abuse patterns early.
- Review and Adjust Policies: Content types and client needs evolve. Periodically review your token expiry and rate limiting settings to ensure they align with current security requirements and user behaviour.
- Layered Security: Emphasise that rate limiting is one layer of a comprehensive strategy. Combine it with strong HMAC tokens, sensible expiry periods, and secure content storage.
WordPress Gatekeeper Pro: Streamlining Gated Content Security
For agencies building client portals, membership sites, or premium resource libraries, managing content access security can be complex. WordPress Gatekeeper Pro simplifies this by providing a comprehensive solution that natively integrates token-based access with robust rate limiting.
The plugin generates cryptographically secure HMAC-SHA256 signed access tokens for any content you mark as "locked." These tokens, delivered via a seamless access request and approval workflow, are then validated by a secure proxy endpoint when users attempt to stream videos or download files. Crucially, Gatekeeper Pro allows you to:
- Configure Rate Limiting: Set a per-hour usage limit for each token, preventing a single shared link from being exploited indefinitely.
- Manage Token Expiry: Define a Time-to-Live (TTL) globally or per-post, with options for unlimited access where appropriate, complementing rate limiting.
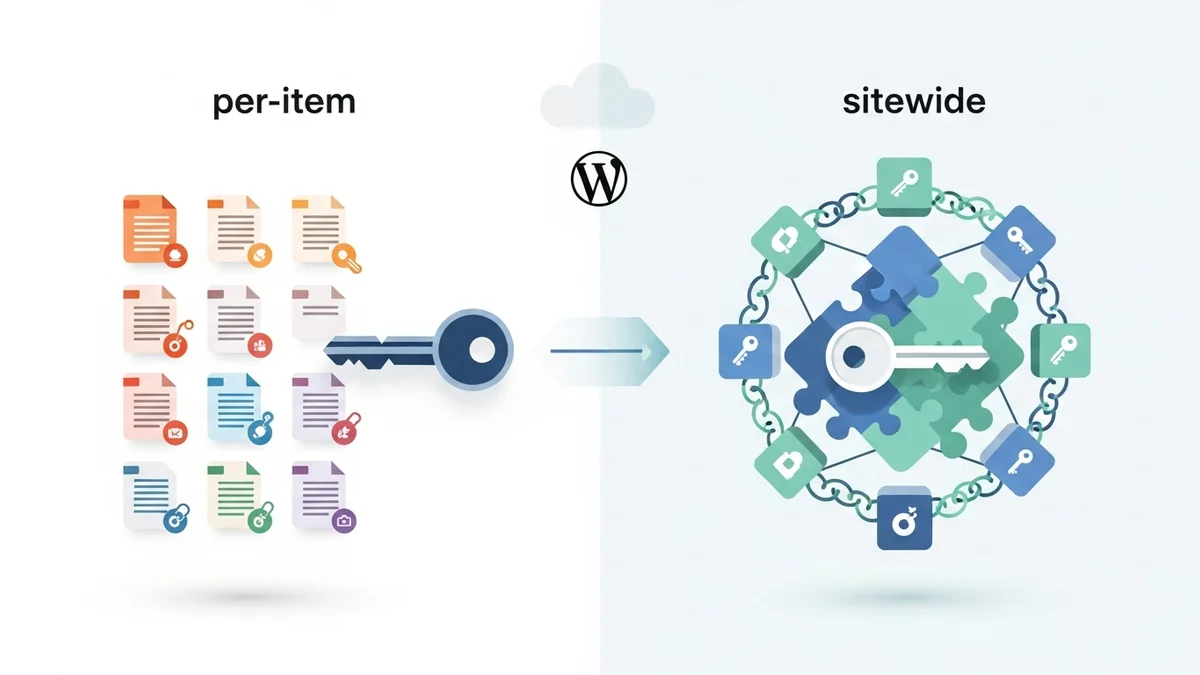
- Choose Access Modes: Implement per-item tokens (each token for one specific resource) or sitewide tokens (one token unlocks all locked content), applying rate limits uniformly across these modes.
This integration provides agencies with a powerful, no-code solution to deliver and manage gated content securely, ensuring clients' valuable assets are protected from unauthorised distribution and link sharing abuse.
Related Articles
Continue your learning with these related resources:
- How to Protect and Restrict Content on WordPress: The Complete Guide (Comprehensive Guide)
- How to Export Content Access Data as CSV From WordPress
- How Long Should You Keep Content Access Logs on WordPress?
- How to Track Who Downloads Files on Your WordPress Site
- WordPress Content Access Analytics: What to Track and Why It Matters for Agencies
- Unleashing the Power of Access Request Data for Lead Qualification on Your WordPress Site
Conclusion
In the digital landscape, protecting premium and confidential content on WordPress is non-negotiable for agencies and their clients. While secure WordPress token based access and token expiry are foundational, rate limiting stands as a critical and often underutilised defence against unauthorised link sharing abuse.
By implementing configurable rate limits on each access token, you significantly reduce the impact of compromised links, maintaining the exclusivity and value of your gated content. For web professionals, understanding and deploying these mechanisms, particularly with powerful tools like WordPress Gatekeeper Pro, is key to delivering truly secure and robust content protection solutions for your clients.